All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
Server for legitimate IP spoofing (not DDoS/amplification)
Hi, I'm looking for a server offer or at least a provider name which allow source IP spoofing.
I have two legitimate reasons to use IP spoofing.
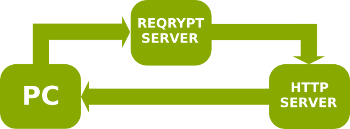
The first is a censorship circumvention system using ReQrypt. ReQrypt software first encrypts and sends first TCP packet to IP spoofing server, the server forwards this packed from client's source IP to destination server, further data transfer between client and destination host within single TCP session is performed without spoofing server. This is faster than proxy and preserves client's IP address.
The second is for my project to traverse NAT without outbound session initiation. It's basically based on pwnat but uses UDP packets on the server side. To connect to the host behind NAT from another NAT client needs to send ICMP TTL Exceeded packet which most NAT drop (but accept if it's incoming). Such ICMP packets would be sent from this server with source IP spoofing.
I'm fine with any configuration. I need at most 256 MB RAM and somewhere about 5 GB HDD. I don't expect traffic to exceed 100 GB per month. The cheaper the better.
Please write PM if you don't want to mention provider in public.

















Comments
Do you need full DNS capabilities? Amplification attacks can be somewhat mitigated if DNS ports are blocked.
Do you have a budget in mind?
If you're going to make an offer, I'm fine if port 53 is blocked. I can configure DNS with dnscrypt.
I'd like to stick with low-end if possible, so $7/mo for VPS at most. I don't need much RAM, HDD, CPU or bandwidth.
It's not worth the risk to any provider to give you this, it is highly abusable. If you truly wish to start a service like this you will want to look at colo and having your own ISP connections.
Can I also block port 123?
If so, then I can do it for $7 in Lithuania. Which OS do you need?
If he's willing to block access to the DNS and NTP ports, then that kind of takes out 90% of the risk IMO.
Needless to say, first sign of abuse, and the server will be cancelled!
Yes it's fine.
Is that VPS? That's the configuration?
Well thank you @valdikss, you've now given Ecatel an excuse to use on the forums.
Francisco
There was one recent thread requesting IP spoofing VPS just in page 2, coincidence?
At least this OP provides better reason though.
That guy straight up wanted it for DOS reasons.
Francisco
There was a guy over at WHT that wanted 100 servers for streaming with ip spoofing enabled, sometime this month.
Keep in mind, just because your DC allows IP spoofing this does NOT mean their upstream will, or that their upstream will. You never get guaranteed spoofing ability.
Oh I think I remember seeing that, he wants to run some massive piracy operation.
Francisco
I didn't know about that, can you please tell more? Is it common to do ingress filtering? How many providers do this?
Telia for example, all Chinese carriers, NTT. Cogent/Level3 probably not.
This is especially the case if the IP you spoof is a directly peered customer of them, so they automatically know this isn't right.
This is crazy. It will stick out like a sore thumb.
If I understand this, you're trying to do peer to peer over UDP, but starting with a server connection. If the p2p part works after setup, why not just have the server hand off the address info instead of spoofing?
Thanks. For ReQrypt I mostly care about Russian connectivity. Do you know something about biggest Russian transit providers like Rascom, Transtelecom, Retn, Megafon, Vimpelcom, Rostelecom?
I doubt my idea is sane now.
Most of these in some way now use ddos-guard here and there, which yes will filter this out. Retn for sure.
I suspect what you try here, if used to circumvent censorship, is illegal in Russia and will get you jail.
Not quite right. Say, server behind NAT sends UDP packets to some constant random address like 3.3.3.3 every 30 seconds. If we send ICMP Time To Live Exceeded to the server from the client that is not behind NAT without any source IP spoofing, server will receive that packet.
Now the problem is that most NATs do not allow to send such ICMP packet since (in terms of linux conntrack) it's neither NEW nor ESTABLISHED or RELATED, it's INVALID and should be dropped. You can't connect to server behind NAT if you as client is also behind NAT. This third-party spoofing server is used to send ICMP packet with source IP address spoofing, while the server behind NAT won't need to connect to any third-party server.
What? Ecatel doesn't allow IP spoofing from MANY years now due to people was abusing of it, they disabled spoofing on all of their range, and their latency from international carrier is one of the best you can find out.
Was ColoCrossing allowing it a while back?
Cogent does not block spoofing? haha, good joke, most of the spoofed typical booter attacks are comming from Cogent ;-)
hm? As i said, Cogent does not block spoofing, I did not say they do. Learn to read english.
Well, "flying" over a text and reading the wrong ones does not mean, that I dont understand English ;-)
I suppose then that only leaves learning to read. If you 'fly over text', that's not exactly reading ;-).
Sure ;-)
Bought a server from @randvegeta. Thanks.
and 27015
and all sort of funny ports people use to reflect from these days.
Well the main ones are DNS and NTP but indeed, there are a bunch of other odd ports. If they can all be blocked then it should mitigate much of the risk. Not to mention the requested only 100GB /m in data transfer, suggesting an average of just 0.15-0.30Mbit.