New on LowEndTalk? Please Register and read our Community Rules.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
All new Registrations are manually reviewed and approved, so a short delay after registration may occur before your account becomes active.
OVH Anti Hack - Can someone explain? (Possible VestaCP Infiltrated)
Hello folks,
I ordered a 2GB KVM from OVH on 21st September. Did install VestaCP and did a dummy SMF installation to see if softacoulous was working. Did the SMF installation on a freenom domain, as I said just to see if it works. Did not touch the server since then. Neither via SSH nor VestaCP admin panel.
Today I received an email from OVH that my service is suspended and contract cancelled. I am pretty sure no one knows the login credentials of this VPS. * demonstrates my server IP at the logs below. Any possible explanation or idea is welcome.
The email is as follows
Dear Customer,
Abnormal activity has been detected on your VPS vps590794.ovh.net.
As this constitutes a breach of contract, your virtual server vps590794.ovh.net
has been blocked.
You will find the logs brought up by our system below, which led to this alert.
- START OF ADDITIONAL INFORMATION -
Attack detail : 92Kpps/54Mbps
dateTime srcIp:srcPort dstIp:dstPort protocol flags packets bytes reason
2018.09.25 06:13:47 CEST *:5093 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:60181 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:31613 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:33875 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:23461 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:12745 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:55352 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:51217 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:41523 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:33135 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:45546 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:54975 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:47277 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:47552 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:41794 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:52731 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:50947 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:19644 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:17319 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
2018.09.25 06:13:47 CEST *:3801 144.0.2.180:80 TCP SYN 16384 1277952 ATTACK:TCP_SYN
















Comments
Did you contact OVH support? They should be able to tell you what`s the next step.
Seems vestacp got again hacked/vulnerable:
https://forum.vestacp.com/viewtopic.php?f=10&t=17641&start=30
About 90 k packets were sent from your server to syn attack some chinese server. What's not to understand?
It seems you didn't understand the basic deal with a VPS: It's your system and YOU are responsible.
@xaoc I created a ticket but no answer so far. It has been around 12 hours.
@AlbaHost Thanks for the clarification. I believe this explains a lot !! Better stick to a paid panel even for a non production environment.
Explanation: Vesta installed, not secured and got hacked.
You need to secure your VPS. I f you dont know what to do, you deserved managed services.
You guys are right but hey this was a development server I bought on last weekend and was planning to work on this weekend.
As AlbaHost said looks like there is a vulnerability. I ve been quite out of all this stuff for a while and the time period I choose to try things out is the time period that my preferred cp is hacked. Fuck my life.
Consider enabling the ovh firewall in the ip section and whitelisting only your own subnet/ip if it's a dev box. If you need help with that gimme a pm and i'll give you some examples.
E: That is when your box gets unsuspended or you get a new box. Not sure if you have access to the firewall for the suspended box's ip at this time. xD
@xaoc
Thanks for recommendations. Will get in touch with you if I ever get access to this box. Can not reinstall, rescue or do anything. Looks like my first experience with OVH is doomed lol
Oh and: stay away from panels. If you know about proper server adminstration do it, if not get a managed VPS.
Adding junk (like panels) NEVER increases security. It always and invariably DEcreases security.
so far there are only wild assumptions to be read.
like @jar already pointed out in the vestacp forums, if that's again a vestacp issue, the assumed hack seem to spread very slowly or is very specific.
I do have quite some vesta installs still on OVH of different age and color, luckily none has been affected so far. will watch over them closely ofc...
What do you use Vesta for that is appealing, specifically? There are better options, that aren't a risk. Either Vesta resulted in a compromised server or you didn't secure the server enough anyways.
Yes. Today(25/09/2018) was hacked VestaCP in the morning. I was thinking of writing a topic on LET, but I did not, because I thought everyone already knew.
30 servers hacked down in the morning.
Morning started with messages from Anti-Hack:
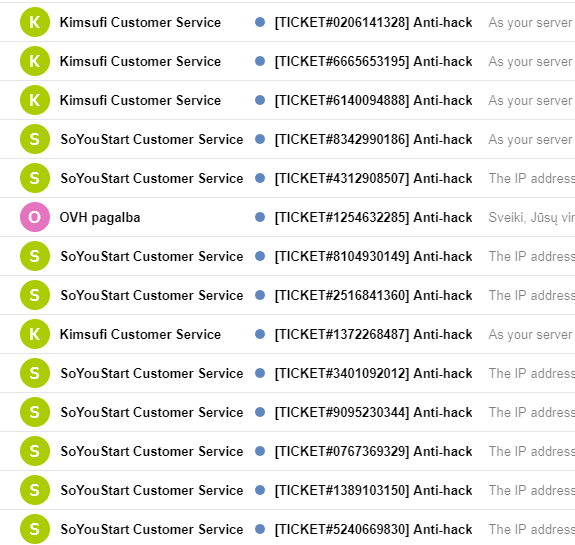
In Online.net too:
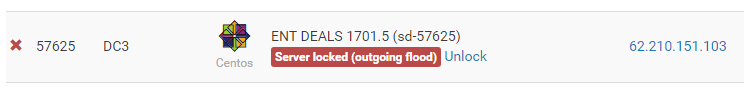
They are generally paid unlocking or free of charge through a ticket.
I sent several servers for diagnostics from VestaCP.
I was away from the scene for quite some time and just wanted to get a few quickies done. Vesta was the last panel I used for my non prodution environments. I knew the interface and such. Nothing special about vestacp actually. Tough luck on my side. Damn...
Do the following as soon as possible:
service vesta stop
Out of curiosity, what's there on this 144.0.2.180 host?
None of my servers were attacked. As a precaution, I stopped all Vesta services.
Damn. I'm done with Vesta
If you tell a room full of people that a virus has been released, then list the symptoms, everyone will develop some of the symptoms.
If you shout vulnerability, everyone with a compromised server will chime in. Servers are compromised every minute of every day. Inevitably several of those people will have software in common.
There is currently no reason to suspect a vestacp vulnerability. Be on alert, of course, but conclusions or significant decision making are not currently logical. There may be a vulnerability, but we don’t have enough data to even suggest more than average daily correlation.
My VestaCP was installed on a freshly installed CentOS 7, on 21st September 2018. Did not alter any settings, if it would be of any help to developers or forensic experts.
Had something happened to a box I have which was running VestaCP for a while. I normally leave the VestaCP UI off, but I forgot to turn it off the last time I did maintenance work.
My host suspended my VPS one day because it was apparently being DDoS-ed, and provided me some logs. Once my host allowed me to work on it and enabled my VM, I stopped the VestaCP GUI, installed CSF and enabled SYN Flood Protection. Changing the SSH port to something non-standard also worked well.
If you don't need the VestaCP GUI, leave it off. That works for me while VestaCP works on a solution.
Am I wrong or all of the compromised boxes are based on Debian 9?
OS doesn't matter. I have a client who was suspended due to the OVH anti-hack detecting an attack, I just checked and the log has the exact same target IP, 144.0.2.180. Definitely the same as the compromised Vesta servers recently.
And which OS was this box using?
My box was on CentOS7
I can confirm same patterns (SYN flood) and same IP for a couple of affected clients during the past 24 hours. I am absolutrly sure it is another vesta related vuln.
I've just shutdown vestacp on my server... I'm on Linode and I've not been hacked yet, but I'm planning to move to EasyEngine
Simple solution that's worked for me is
(1) change SSH to a non-standard port
(2) Disable or firewall the GUI.
By default the GUI comes up on https://server:8083/
You can login to https://server:8083/list/firewall/ and SUSPEND the rule for port 8083.
If you need access to GUI this can still be accomplished by SSH forwarding/tunneling port 8083 and you'll be able to access the GUI at:
https://localhost:8083/
It seems many VestaCP servers get hacked. But is it only those servers on OVH get suspended?